Exam Details
Exam Code
:AZ-800Exam Name
:Administering Windows Server Hybrid Core InfrastructureCertification
:Microsoft CertificationsVendor
:MicrosoftTotal Questions
:247 Q&AsLast Updated
:Apr 01, 2025
Microsoft Microsoft Certifications AZ-800 Questions & Answers
-
Question 141:
You have an Azure virtual machine named Server1 that runs a network management application. Server1 has the following network configurations:
1.
Network interface: Nic1
2.
IP address: 10.1.1.1/24
3.
Connected to: Vnet1/Subnet1
You need to connect Server1 to an additional subnet named Vnet1/Subnet2.
What should you do?
A. Modify the IP configurations of Nic1.
B. Add an IP configuration to Nic1.
C. Add a network interface to Server1.
D. Create a private endpoint on Subnet2.
-
Question 142:
Your network contains an Active Directory domain named contoso.com. The domain contains the computers shown in the following table.
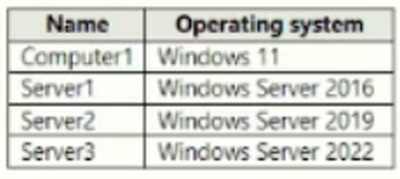
On Server3, you create a Group Policy Object (GPO) named GPO1 and link GPO1 to contoso.com. GPO1 includes a shortcut preference named Shortcut1 that has item-level targeting configured as shown in the following exhibit.
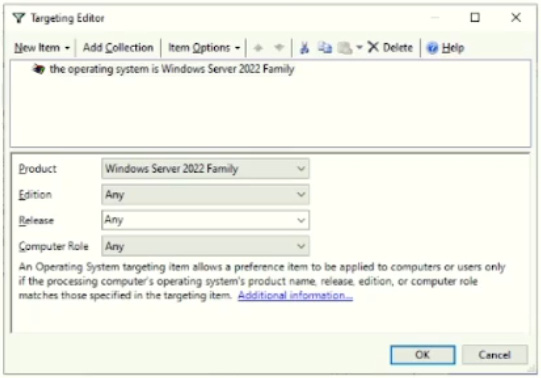
To which computer will Shortcut1 be applied?
A. Server3 only
B. Computer1 and Server3 only
C. Server2 and Server3 only
D. Server1, Server2, and Server3 only
-
Question 143:
You have an on-premises Active Directory Domain Services (AD DS) domain that syncs with an Azure Active Directory (Azure AD) tenant. Group writeback is enabled in Azure AD Connect.
The AD DS domain contains a server named Server1. Server1 contains a shared folder named share1.
You have an Azure Storage account named storage2 that uses Azure AD-based access control. The storage2 account contains a share named share2.
You need to create a security group that meets the following requirements:
1.
Can contain users from the AD DS domain
2.
Can be used to authorize user access to share1 and share2 What should you do?
A. In the Azure AD tenant, create a security group that has assigned membership.
B. In the AD DS domain, create a universal security group.
C. In the Azure AD tenant, create a security group that has dynamic membership.
D. In the Azure AD tenant, create a Microsoft 365 group.
-
Question 144:
Your network contains an Active Directory Domain Services (AD DS) forest. The forest contains three domains. Each domain contains 10 domain controllers.
You plan to store a DNS zone in a custom Active Directory partition.
You need to create the Active Directory partition for the zone. The partition must replicate to only four of the domain controllers.
What should you use?
A. Windows Admin Center
B. DNS Manager
C. Active Directory Sites and Services
D. ntdsutil.exe
-
Question 145:
Your network contains an Active Directory forest. The forest contains two domains named contoso.com and east.contoso.com and the servers shown in the following table.
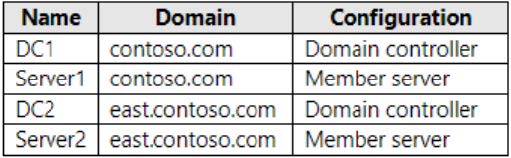
Contoso.com contains a user named User1.
You add User1 to the built-in Backup Operators group in contoso.com.
Which servers can User1 back up?
A. DC1 only
B. Server1 only
C. DC1 and DC2 only
D. DC1 and Server1 only
E. DC1, DC2, Server1, and Server2
-
Question 146:
You have a server named Server1 that runs Windows Server.
You plan to host applications in Windows containers.
You need to configure Server1 to run containers.
What should you install?
A. Windows Admin Center
B. Docker
C. the Windows Subsystem for Linux
D. Hyper-V
-
Question 147:
Your network contains an Active Directory Domain Services (AD DS) forest named contoso.com. The forest root domain contains a server named server1.contoso.com.
A two-way forest trust exists between the contoso.com forest and an AD DS forest named fabrikam.com. The fabrikam.com forest contains 10 child domains.
You need to ensure that only the members of a group named fabrikam\Group1 can authenticate to server1.contoso.com.
What should you do first?
A. Add fabrikam\Group1 to the local Users group on server1.contoso.com.
B. Enable SID filtering for the trust.
C. Enable Selective authentication for the trust.
D. Change the trust to a one-way external trust.
-
Question 148:
You have a server named Server1 that runs Windows Server and contains two drives named C and D. Server1 hosts multiple file shares.
You enable Data Deduplication on drive D and select the General purpose file server workload.
You need to minimize the space consumed by files that were recently modified or deleted.
What should you do?
A. Run the set-dedupvolume cmdlet and configure the scrubbing job.
B. Run the Set-DedupSchedule Cmdlet and configure a GarbageCollection job.
C. Run the set-Dedupvoiume cmdlet and configure the InputOutputScale settings.
D. Run the Set-DedupSchedule cmdlet and configure the optimization job.
-
Question 149:
Your network contains an Active Directory Domain Services (AD DS) domain.
The domain contains a user named User1 and the servers shown in the following table.
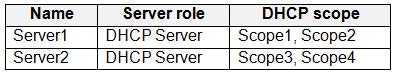
You need to ensure that User1 can manage only Scope1 and Scope3. What should you do?
A. Add User1 to the DHCP Administrators group on Server1 and Server2.
B. Implement IP Address Management (IPAM).
C. Add User1 to the DHCP Administrators domain local group.
D. Implement Windows Admin Center and add connections to Server1 and Server2.
-
Question 150:
You have an Azure subscription that contains a virtual machine named VM1 as shown in the following exhibit.
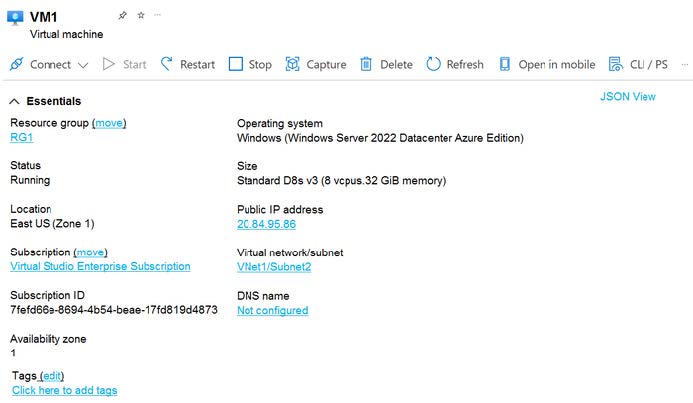
The subscription has the disks shown in the following table.
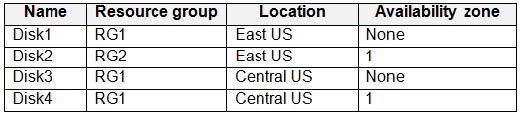
Which disks can you attach as data disks to VM1?
A. Disk2 only
B. Disk4 only
C. Disk1 and Disk2 only
D. Disk2 and Disk4 only
E. Disk1, Disk3, and Disk4 only
F. Disk1, Disk2, Disk3. and Disk4
Related Exams:
62-193
Technology Literacy for Educators70-243
Administering and Deploying System Center 2012 Configuration Manager70-355
Universal Windows Platform – App Data, Services, and Coding Patterns77-420
Excel 201377-427
Excel 2013 Expert Part One77-725
Word 2016 Core Document Creation, Collaboration and Communication77-726
Word 2016 Expert Creating Documents for Effective Communication77-727
Excel 2016 Core Data Analysis, Manipulation, and Presentation77-728
Excel 2016 Expert: Interpreting Data for Insights77-731
Outlook 2016 Core Communication, Collaboration and Email Skills
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Microsoft exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your AZ-800 exam preparations and Microsoft certification application, do not hesitate to visit our Vcedump.com to find your solutions here.