Exam Details
Exam Code
:CV0-003Exam Name
:CompTIA Cloud+Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:503 Q&AsLast Updated
:Mar 26, 2025
CompTIA CompTIA Certifications CV0-003 Questions & Answers
-
Question 111:
A company would like to migrate its current on-premises workloads to the public cloud. The current platform requires at least 80 instances running at all times to work properly. The company wants the workload to be highly available, even if the cloud provider loses one region due to a catastrophe, and the costs to be kept to a minimum. Which of the following strategies should the company implement?
A. Create /25 subnets in two regions and run 80 instances on each one.
B. Create /26 subnets in two regions and run 40 instances on each one.
C. Create /26 subnets in three regions and run 40 instances on each one
D. Create /26 subnets in three regions and run 80 instances on each one.
-
Question 112:
An enterprise recently upgraded the memory of its on-premises VMs from 8GB to 16GB. However, users are not experiencing any performance benefit. Which of the following is the MOST likely reason?
A. Insufficient memory on the hypervisor
B. Operating system memory limit
C. Memory mismatch error
D. Dynamic memory allocation
-
Question 113:
A development team recently completed testing changes to a company's web-based CMS in the sandbox environment. The cloud administrator deployed these CMS application changes to the staging environment as part of the next phase in the release life cycle. The deployment was successful, but after deploying the CMS application, the web page displays an error message stating the application is unavailable. After reviewing the application logs, the administrator sees an error message that the CMS is unable to connect to the database. Which of the following is the BEST action for the cloud administrator to perform to resolve the issue?
A. Modify the deployment script to delete and recreate the database whenever the CMS application is deployed.
B. Modify the ACL to allow the staging environment to access the database in the sandbox environment.
C. Modify the CMS application deployment to use the previous version and redeploy the application.
D. Modify the configuration settings of the CMS application to connect to the database in the current environment.
-
Question 114:
A cloud administrator has created a new asynchronous workflow lo deploy VMs to the cloud in bulk. When the workflow is tested for a single VM, it completes successfully. However, if the workflow is used to create 50 VMs at once, the job fails. Which of the following is the MOST likely cause of the issue? (Choose two.)
A. Incorrect permissions
B. Insufficient storage
C. Billing issues with the cloud provider
D. No connectivity to the public cloud
E. Expired API token
F. Disabled autoscaling
-
Question 115:
A systems administrator is asked to implement a new three-host cluster. The cloud architect specifies this should be a testing environment, and the budget is limited. The estimated resource consumption for each application is as follows:
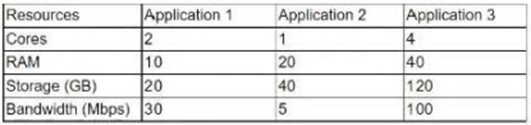
A. Three public cloud hosts with four cores 120GB of RAM 100GB of storage 1Gbps
B. Three public cloud hosts with six cores 80GB of RAM 180GB of storage 150Mbps
C. Three public cloud hosts with six cores 80GB of RAM 1TB of storage 200Mbps
D. Four public cloud hosts with four cores 140GB of RAM 200GB of storage
-
Question 116:
A systems administrator is about to deploy a new VM to a cloud environment. Which of the following will the administrator MOST likely use to select an address for the VM?
A. CDN
B. DNS
C. NTP
D. IPAM
-
Question 117:
A company had a system compromise, and the engineering team resolved the issue after 12 hours. Which of the following information will MOST likely be requested by the Chief Information Officer (CIO) to understand the issue and its resolution?
A. A root cause analysis
B. Application documentation
C. Acquired evidence
D. Application logs
-
Question 118:
An organization has a public-facing API that is hosted on a cloud provider. The API performs slowly at times. Which of the following technologies should the cloud administrator apply to provide speed acceleration and a secure connection?
A. WAF
B. EDR
C. IDS
D. HIPS
E. SSL
-
Question 119:
A production engineer is configuring a new application, which is running in containers, that requires access to a database. Which of the following methods will allow the application to authenticate to the database in the MOST secure way?
A. Store the credentials in a variable on every worker node
B. Store the credentials on a shared volume using whole-disk encryption
C. Store the credentials in a configuration file using SHA-256 inside the container image
D. Store the credentials using the orchestrator secret manager
-
Question 120:
A systems administrator wants to verify the word "qwerty" has not been used as a password on any of the administrative web consoles in a network. Which of the following will achieve this goal?
A. A service availability scan
B. An agent-based vulnerability scan
C. A default and common credentialed scan
D. A network port scan
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+CLO-002
CompTIA Cloud Essentials+CS0-002
CompTIA Cybersecurity Analyst (CySA+)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CV0-003 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.