Exam Details
Exam Code
:ECSAV10Exam Name
:EC-Council Certified Security Analyst (ECSA) v10Certification
:EC-COUNCIL CertificationsVendor
:EC-COUNCILTotal Questions
:354 Q&AsLast Updated
:Mar 24, 2025
EC-COUNCIL EC-COUNCIL Certifications ECSAV10 Questions & Answers
-
Question 281:
An employee is trying to access the internal website of his company. When he opened a webpage, he received an error message notifying "Proxy Authentication Required." He approached the IT department in the company and reported the issue. The IT staff explained him that this is an HTTP error indicating that the server is unable to process the request due to lack of appropriate client's authentication credentials for a proxy server that is processing the requests between the clients and the server. Identify the HTTP error code corresponding to the above error message received by the employee?
A. 415
B. 417
C. 407
D. 404
-
Question 282:
Arrange the WEP cracking process in the correct order:
I. aireplay-ng -1 0 -e SECRET_SSID -a 1e:64:51:3b:ff:3e -h a7:71:fe:8e:d8:25 eth1
II. aircrack-ng -s capture.ivs
III. airmon-ng start eth1
IV.
airodump-ng --ivs --write capture eth1
V.
aireplay-ng -3 -b 1e:64:51:3b:ff:3e -h a7:71:fe:8e:d8:25 eth1
A.
IV-->I-->V-->III-->II
B.
III-->IV-->V-->II-->I
C.
III-->IV-->I-->V-->II
D.
IV-->I-->V-->III-->II
-
Question 283:
An attacker with a malicious intention decided to hack confidential data from the target organization. For acquiring such information, he started testing IoT devices that are connected to the target network. He started monitoring the network traffic passing between the IoT devices and the network to verify whether credentials are being transmitted in clear text. Further, he also tried to crack the passwords using well-known keywords across all the interfaces. Which of the following IoT threats the attacker is trying to exploit?
A. Poor physical security
B. Poor authentication
C. Privacy concerns
D. Insecure firmware
-
Question 284:
Allen and Greg, after investing in their startup company called Zamtac Ltd., developed a new web application for their company. Before hosting the application, they want to test the robustness and immunity of the developed web application against attacks like buffer overflow, DOS, XSS, and SQL injection. What is the type of the web application security test Allen and Greg should perform?
A. Web fuzzing
B. Web crawling
C. Web spidering
D. Web mirroring
-
Question 285:
George, an ex-employee of Netabb Ltd. with bruised feelings due to his layoff, tries to take revenge against the company. He randomly tried several attacks against the organization. As some of the employees used weak passwords to their user accounts, George was successful in cracking the user accounts of several employees with the help of a common passwords file. What type of password cracking attack did George perform?
A. Hybrid attack
B. Dictionary attack
C. Brute forcing attack
D. Birthday attack
-
Question 286:
James, a research scholar, received an email informing that someone is trying to access his Google account from an unknown device. When he opened his email message, it looked like a standard Google notification instructing him to click the link below to take further steps. This link was redirected to a malicious webpage where he was tricked to provide Google account credentials. James observed that the URL began with www.translate.google.com giving a legitimate appearance. In the above scenario, identify the type of attack being performed on James' email account?
A. SMiShing
B. Dumpster diving
C. Phishing
D. Vishing
-
Question 287:
What is the objective of the following bash script?
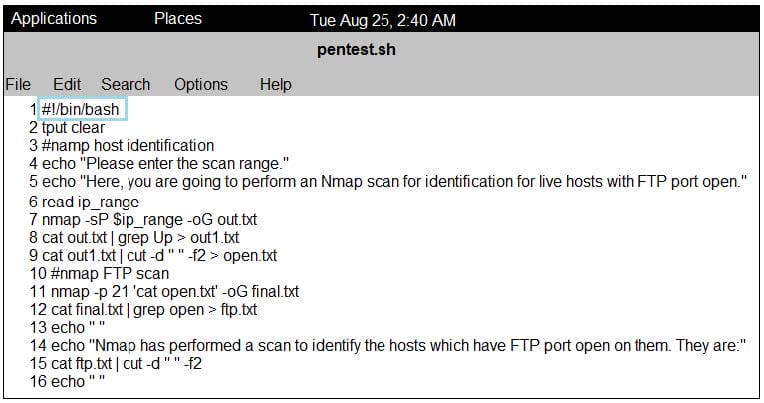
A. It gives a list of IP addresses that have an FTP port open
B. It tries to connect to FTP port on a target machine C. It checks if a target host has the FTP port open and quits
D. It checks if an FTP port on a target machine is vulnerable to arracks
-
Question 288:
ABC Technologies, a large financial company, hired a penetration tester to do physical penetration testing.
On the first day of his assignment, the penetration tester goes to the company posing as a repairman and
starts checking trash bins to collect the sensitive information.
What is the penetration tester trying to do?
A. Trying to attempt social Engineering using phishing
B. Trying to attempt social engineering by shoulder surfing
C. Trying to attempt social engineering by eavesdropping
D. Trying to attempt social engineering by dumpster diving
-
Question 289:
Dale is a network admin working in Zero Faults Inc. Recently the company's network was compromised and is experiencing very unusual traffic. Dale checks for the problem that compromised the network. He performed a penetration test on the network's IDS and identified that an attacker sent spoofed packets to a broadcast address in the network. Which of the following attacks compromised the network?
A. ARP Spoofing
B. Amplification attack
C. MAC Spoofing
D. Session hijacking
-
Question 290:
You are enumerating a target system. Which of the following PortQry commands will give a result similar to the screenshot below:
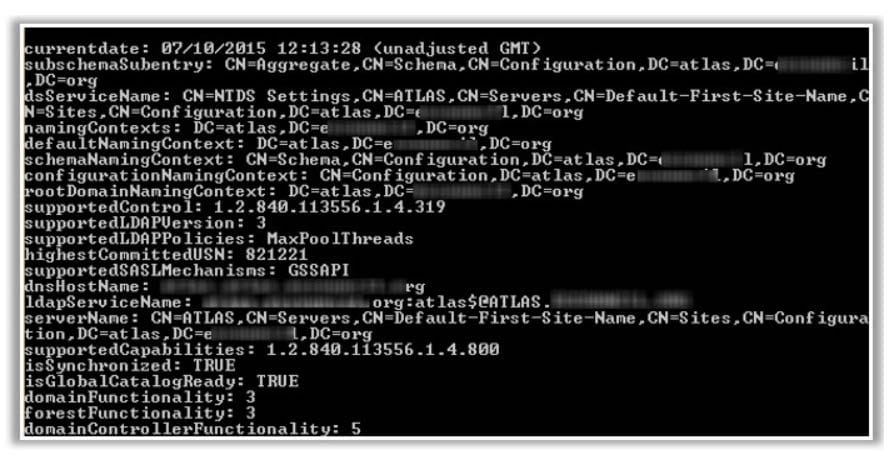
A. portqry -n myserver -p udp -e 389
B. portqry -n myserver -p udp -e 123
C. portqry -n myserver -p TCP -e 389
D. portqry -n myserver -p TCP -e 123
Related Exams:
112-51
EC-Council Certified Network Defense Essentials (NDE)212-77
EC-Council Certified Linux Security212-81
EC-Council Certified Encryption Specialist (ECES)212-82
EC-Council Certified Cybersecurity Technician (C|CT)212-89
EC-Council Certified Incident Handler (ECIH)312-38
EC-Council Certified Network Defender (CND)312-39
EC-Council Certified SOC Analyst (CSA)312-40
EC-Council Certified Cloud Security Engineer (CCSE)312-49
ECCouncil Computer Hacking Forensic Investigator (V9)312-49V10
EC-Council Certified Computer Hacking Forensic Investigator (V10)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your ECSAV10 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.