Exam Details
Exam Code
:ECSAV10Exam Name
:EC-Council Certified Security Analyst (ECSA) v10Certification
:EC-COUNCIL CertificationsVendor
:EC-COUNCILTotal Questions
:354 Q&AsLast Updated
:Mar 24, 2025
EC-COUNCIL EC-COUNCIL Certifications ECSAV10 Questions & Answers
-
Question 271:
Jeffry, a penetration tester in Repotes Solutions Pvt. Ltd., is facing a problem in testing the firewall. By consulting other penetration testers and considering other penetration testing approaches, he was able to take critical decisions on how to test the firewall; he was finally successful in testing the firewall for vulnerabilities. In which of the following sections of penetration testing report will Jeffry mention the above situation?
A. Timeline
B. Evaluation purpose
C. Assumptions
D. System description
-
Question 272:
Adam found a pen drive in his company's parking lot. He connected it to his system to check the content. On the next day, he found that someone has logged into his company email account and sent some emails. What type of social engineering attack has Adam encountered?
A. Media Dropping
B. Phishing
C. Eaves Dropping
D. Dumpster Diving
-
Question 273:
Russel, a penetration tester after performing the penetration testing, wants to create a report so that he can provide details of the testing process and findings of the vulnerabilities to the management. Russel employs the commonly available vulnerability scoring framework called Common Vulnerability Scoring System (CVSS) v3.0 ratings for grading the severity and risk level of identified vulnerabilities in the report. For a specific SMB-based vulnerability, Russel assigned a score of 8.7. What is the level of risk or level of severity of the SMB vulnerability as per CVSS v3.0 for the assigned score?
A. Critical
B. Low
C. Medium
D. High
-
Question 274:
Lee has established a new startup where they develop android applications. In order to meet memory requirements of the company, Lee has hired a Cloud Service Provider, who offered memory space along with virtual systems. Lee was dissatisfied with their service and wanted to move to another CSP, but was denied as a part of the contract, which reads that the user cannot switch to another CSP. What is this condition called?
A. Virtualization
B. Lock-in
C. Resource Isolation
D. Lock-up
-
Question 275:
An organization hosted a website to provide services to its customers. A visitor of this website has reported a complaint to the organization that they are getting an error message with code 502 when they are trying to access the website. This issue was forwarded to the IT department in the organization. The IT department identified the reason behind the error and started resolving the issue by checking whether the server is overloaded, whether the name resolution is working properly, whether the firewall is configured properly, etc. Identify the error message corresponding to code 502 that the visitors obtained when they tried to access the organization's website?
A. Bad request
B. Forbidden
C. Internal error
D. Bad gateway
-
Question 276:
Which of the following statements highlights the difference between a vulnerability assessment and a penetration test?
A. A vulnerability assessment identifies and ranks the vulnerabilities, and a penetration test exploits the identified vulnerabilities for validation and to determine impact.
B. A vulnerability assessment focuses on low severity vulnerabilities and pen testing focuses on high severity vulnerabilities.
C. A vulnerability assessment requires only automated tools to discover the vulnerabilities whereas pen testing also involves manual discovery of vulnerabilities.
D. A vulnerability assessment is performed only on software components of an information system, whereas pen testing is performed on all hardware and software components of the system.
-
Question 277:
Rebecca works as a Penetration Tester in a security service firm named Xsecurity. Rebecca placed a sniffer on a subnet residing deep inside the client's network. She used the Firewalk tool to test the security of the company's network firewall. After the test, when Rebecca checked the sniffer logs, she was unable to see any traffic produced by the Firewalk tool. What is the reason for this?
A. Rebecca does not see any of the Firewalk traffic because it sets all packets with a TTL of one.
B. Network sniffers cannot detect Firewalk so that is why none of the traffic appears.
C. Firewalk cannot pass through firewalls.
D. She cannot see the traffic because Firewalk sets all packets with a TTL of zero.
-
Question 278:
George, a reputed ethical hacker and penetration testing consultant, was hired by FNB Services, a startup financial services company, to audit the security of their web applications. During his investigation, George discovered that the company's website is vulnerable to blind SQL injection attacks. George entered a custom SQL query in a form located on the vulnerable page which resulted in a back-end SQL query similar to the one given below: http://fnb.com/forms/?id=1+AND+555=if(ord(mid((select+pass from+users+limit+0,1),1,2))= 97,555,777) What is George trying to achieve with this custom SQL query?
A. George is searching for the first character of all the table entries
B. George is searching for the second character of the first table entry
C. George is searching for the first character of the second table entry
D. George is searching for the first character of the first table entry
-
Question 279:
Recently, Jacob was assigned a project to test the perimeter security of one of a client. As part of the
project, Jacob wants to test whether or not a particular port on the firewall is open or closed. He used the
hping utility with the following syntax:
#hping –S –c 1 –p
-t What response will indicate the particular port is allowed in the firewall?
A. Host Unreachable
B. TTL Exceeded
C. No Response
D. ICMP Port Unreachable
-
Question 280:
During scanning of a test network, Paul sends TCP probe packets with the ACK flag set to a remote device
and then analyzes the header information (TTL and WINDOW field) of the received RST packets to find
whether the port is open or closed.
Analyze the scanning result below and identify the open port.
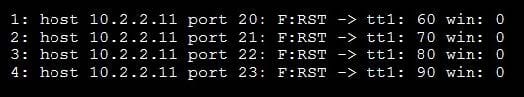
A. Port 22
B. Port 23
C. Port 21
D. Port 20
Related Exams:
112-51
EC-Council Certified Network Defense Essentials (NDE)212-77
EC-Council Certified Linux Security212-81
EC-Council Certified Encryption Specialist (ECES)212-82
EC-Council Certified Cybersecurity Technician (C|CT)212-89
EC-Council Certified Incident Handler (ECIH)312-38
EC-Council Certified Network Defender (CND)312-39
EC-Council Certified SOC Analyst (CSA)312-40
EC-Council Certified Cloud Security Engineer (CCSE)312-49
ECCouncil Computer Hacking Forensic Investigator (V9)312-49V10
EC-Council Certified Computer Hacking Forensic Investigator (V10)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your ECSAV10 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.