Exam Details
Exam Code
:ECSAV10Exam Name
:EC-Council Certified Security Analyst (ECSA) v10Certification
:EC-COUNCIL CertificationsVendor
:EC-COUNCILTotal Questions
:354 Q&AsLast Updated
:Mar 24, 2025
EC-COUNCIL EC-COUNCIL Certifications ECSAV10 Questions & Answers
-
Question 71:
Which of the following policy forbids everything with strict restrictions on all usage of the company systems and network?
A. Information-Protection Po
B. Paranoid Policy
C. Promiscuous Policy
D. Prudent Policy
-
Question 72:
After passively scanning the network of Department of Defense (DoD), you switch over to active scanning to identify live hosts on their network. DoD is a large organization and should respond to any number of scans. You start an ICMP ping sweep by sending an IP packet to the broadcast address. Only five hosts responds to your ICMP pings; definitely not the number of hosts you were expecting. Why did this ping sweep only produce a few responses?
A. A switched network will not respond to packets sent to the broadcast address
B. Only IBM AS/400 will reply to this scan
C. Only Unix and Unix-like systems will reply to this scan
D. Only Windows systems will reply to this scan
-
Question 73:
Harold wants to set up a firewall on his network but is not sure which one would be the most appropriate.
He knows he needs to allow FTP traffic to one of the servers on his network, but he wants to only allow
FTP-PUT.
Which firewall would be most appropriate for Harold?
A. Application-level proxy firewall
B. Data link layer firewall
C. Packet filtering firewall
D. Circuit-level proxy firewall
-
Question 74:
Which of the following are the default ports used by NetBIOS service?
A. 135, 136, 139, 445
B. 134, 135, 136, 137
C. 137, 138, 139, 140
D. 133, 134, 139, 142
-
Question 75:
You are assisting a Department of Defense contract company to become compliant with the stringent
security policies set by the DoD. One such strict rule is that firewalls must only allow incoming connections
that were first initiated by internal computers.
What type of firewall must you implement to abide by this policy?
A. Circuit-level proxy firewall
B. Packet filtering firewall
C. Application-level proxy firewall
D. Statefull firewall
-
Question 76:
Julia is a senior security analyst for Berber Consulting group. She is currently working on a contract for a small accounting firm in Florida; They have given her permission to perform social engineering attacks on the company to see if their in-house training did any good. Julia calls the main number for the accounting firm and talks to the receptionist. Julia says that she is an IT technician from the company's main office in Iowa; She states that she needs the receptionist's network username and password to troubleshoot a problem they are having. Julia says that Bill Hammond, the CEO of the company, requested this information. After hearing the name of the CEO, the receptionist gave Julia all the information she asked for. What principal of social engineering did Julia use?
A. Reciprocation
B. Friendship/Liking
C. Social Validation
D. Scarcity
-
Question 77:
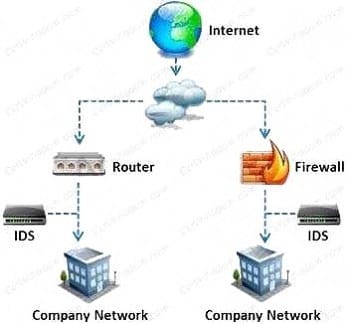
What is a difference between host-based intrusion detection systems (HIDS) and network-based intrusion detection systems (NIDS)?
A. NIDS are usually a more expensive solution to implement compared to HIDS.
B. Attempts to install Trojans or backdoors cannot be monitored by a HIDS whereas NIDS can monitor and stop such intrusion events.
C. NIDS are standalone hardware appliances that include network intrusion detection capabilities whereas HIDS consist of software agents installed on individual computers within the system.
D. HIDS requires less administration and training compared to NIDS.
-
Question 78:
Metasploit framework in an open source platform for vulnerability research, development, and penetration testing. Which one of the following metasploit options is used to exploit multiple systems at once?
A. NinjaDontKill
B. NinjaHost
C. RandomNops
D. EnablePython
-
Question 79:
Which of the following scan option is able to identify the SSL services?
A. -sS
B. -sV
C. -sU
D. -sT
-
Question 80:
Which of the following reports provides a summary of the complete pen testing process, its outcomes, and recommendations?
A. Vulnerability Report
B. Executive Report
C. Client-side test Report
D. Host Report
Related Exams:
112-51
EC-Council Certified Network Defense Essentials (NDE)212-77
EC-Council Certified Linux Security212-81
EC-Council Certified Encryption Specialist (ECES)212-82
EC-Council Certified Cybersecurity Technician (C|CT)212-89
EC-Council Certified Incident Handler (ECIH)312-38
EC-Council Certified Network Defender (CND)312-39
EC-Council Certified SOC Analyst (CSA)312-40
EC-Council Certified Cloud Security Engineer (CCSE)312-49
ECCouncil Computer Hacking Forensic Investigator (V9)312-49V10
EC-Council Certified Computer Hacking Forensic Investigator (V10)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your ECSAV10 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.