Exam Details
Exam Code
:200-201Exam Name
:Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)Certification
:CyberOps AssociateVendor
:CiscoTotal Questions
:406 Q&AsLast Updated
:Mar 30, 2025
Cisco CyberOps Associate 200-201 Questions & Answers
-
Question 81:
What should an engineer use to aid the trusted exchange of public keys between user tom0411976943 and dan1968754032?
A. central key management server
B. web of trust
C. trusted certificate authorities
D. registration authority data
-
Question 82:
Which data type is necessary to get information about source/destination ports?
A. statistical data
B. session data
C. connectivity data
D. alert data
-
Question 83:
Which two elements of the incident response process are stated in NIST Special Publication 800-61 r2? (Choose two.)
A. detection and analysis
B. post-incident activity
C. vulnerability management
D. risk assessment
E. vulnerability scoring
-
Question 84:
Which filter allows an engineer to filter traffic in Wireshark to further analyze the PCAP file by only showing the traffic for LAN 10.11.x.x, between workstations and servers without the Internet?
A. src=10.11.0.0/16 and dst=10.11.0.0/16
B. ip.src==10.11.0.0/16 and ip.dst==10.11.0.0/16
C. ip.src=10.11.0.0/16 and ip.dst=10.11.0.0/16
D. src==10.11.0.0/16 and dst==10.11.0.0/16
-
Question 85:
Which attack represents the evasion technique of resource exhaustion?
A. SQL injection
B. man-in-the-middle
C. bluesnarfing
D. denial-of-service
-
Question 86:
A security engineer deploys an enterprise-wide host/endpoint technology for all of the company's corporate PCs. Management requests the engineer to block a selected set of applications on all PCs.
Which technology should be used to accomplish this task?
A. application whitelisting/blacklisting
B. network NGFW
C. host-based IDS
D. antivirus/antispyware software
-
Question 87:
Which event is a vishing attack?
A. obtaining disposed documents from an organization
B. using a vulnerability scanner on a corporate network
C. setting up a rogue access point near a public hotspot
D. impersonating a tech support agent during a phone call
-
Question 88:
An analyst is using the SIEM platform and must extract a custom property from a Cisco device and capture the phrase, "File: Clean." Which regex must the analyst import?
A. File: Clean
B. ^Parent File Clean$
C. File: Clean (.*)
D. ^File: Clean$
-
Question 89:
How does an attacker observe network traffic exchanged between two users?
A. port scanning
B. man-in-the-middle
C. command injection
D. denial of service
-
Question 90:
Refer to the exhibit.
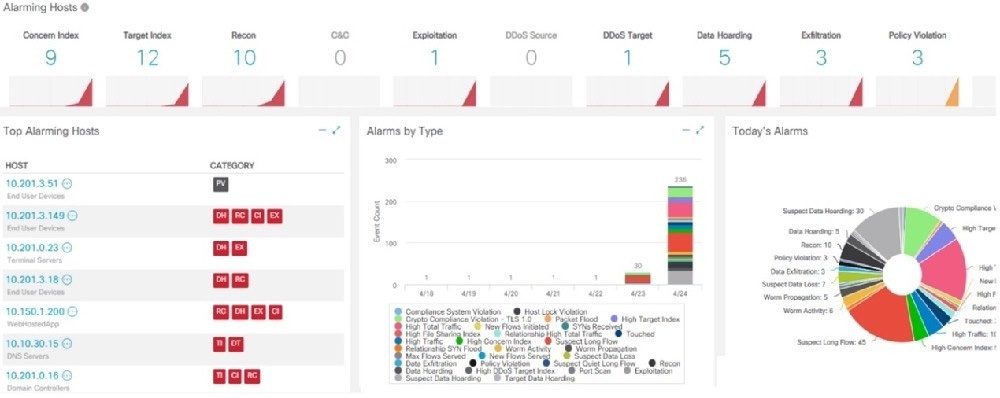
What is the potential threat identified in this Stealthwatch dashboard?
A. A policy violation is active for host 10.10.101.24.
B. A host on the network is sending a DDoS attack to another inside host.
C. There are three active data exfiltration alerts.
D. A policy violation is active for host 10.201.3.149.
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Cisco exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 200-201 exam preparations and Cisco certification application, do not hesitate to visit our Vcedump.com to find your solutions here.