Exam Details
Exam Code
:ECSAv8Exam Name
:EC-Council Certified Security Analyst (ECSA) v8Certification
:EC-COUNCIL CertificationsVendor
:EC-COUNCILTotal Questions
:200 Q&AsLast Updated
:Mar 30, 2025
EC-COUNCIL EC-COUNCIL Certifications ECSAv8 Questions & Answers
-
Question 81:
Due to illegal inputs, various types of TCP stacks respond in a different manner. Some IDSs do not take into account the TCP protocol's urgency feature, which could allow testers to evade the IDS.

Penetration tester needs to try different combinations of TCP flags (e.g. none, SYN/FIN, SYN/RST, SYN/ FIN/ACK, SYN/RST/ACK, and All Flags) to test the IDS.
Which of the following TCP flag combinations combines the problem of initiation, midstream, and termination flags with the PSH and URG?
A. SYN/RST/ACK
B. SYN/FIN/ACK
C. SYN/FIN
D. All Flags
-
Question 82:
Traffic on which port is unusual for both the TCP and UDP ports?
A. Port 81
B. Port 443
C. Port 0
D. Port21
-
Question 83:
Which of the following statements is true about Multi-Layer Intrusion Detection Systems (mIDSs)?
A. Decreases consumed employee time and increases system uptime
B. Increases detection and reaction time
C. Increases response time
D. Both a and c
-
Question 84:
Hackers today have an ever-increasing list of weaknesses in the web application structure at their disposal, which they can exploit to accomplish a wide variety of malicious tasks.

New flaws in web application security measures are constantly being researched, both by hackers and by security professionals. Most of these flaws affect all dynamic web applications whilst others are dependent on specific application technologies. In both cases, one may observe how the evolution and refinement of web technologies also brings about new exploits which compromise sensitive databases, provide access to theoretically secure networks, and pose a threat to the daily operation of online businesses.
What is the biggest threat to Web 2.0 technologies?
A. SQL Injection Attacks
B. Service Level Configuration Attacks
C. Inside Attacks
D. URL Tampering Attacks
-
Question 85:
What sort of vulnerability assessment approach starts by building an inventory of protocols found on the machine?
A. Inference-based Assessment
B. Service-based Assessment Solutions
C. Product-based Assessment Solutions
D. Tree-based Assessment
-
Question 86:
Which type of vulnerability assessment tool provides security to the IT system by testing for vulnerabilities in the applications and operation system?
A. Active/Passive Tools
B. Application-layer Vulnerability Assessment Tools
C. Location/Data Examined Tools
D. Scope Assessment Tools
-
Question 87:
Information gathering is performed to:
i) Collect basic information about the target company and its network
ii) Determine the operating system used, platforms running, web server versions, etc.
iii) Find vulnerabilities and exploits Which of the following pen testing tests yields information about a company's technology infrastructure?
A. Searching for web page posting patterns
B. Analyzing the link popularity of the company's website
C. Searching for trade association directories
D. Searching for a company's job postings
-
Question 88:
A penetration tester performs OS fingerprinting on the target server to identify the operating system used on the target server with the help of ICMP packets.
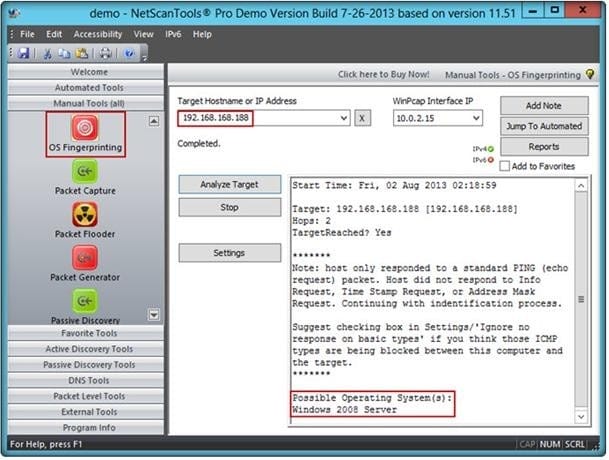
While performing ICMP scanning using Nmap tool, message received/type displays "3 ?Destination Unreachable[5]" and code 3.
Which of the following is an appropriate description of this response?
A. Destination port unreachable
B. Destination host unavailable
C. Destination host unreachable
D. Destination protocol unreachable
-
Question 89:
What is the difference between penetration testing and vulnerability testing?

A. Penetration testing goes one step further than vulnerability testing; while vulnerability tests check for known vulnerabilities, penetration testing adopts the concept of `in-depth ethical hacking'
B. Penetration testing is based on purely online vulnerability analysis while vulnerability testing engages ethical hackers to find vulnerabilities
C. Vulnerability testing is more expensive than penetration testing
D. Penetration testing is conducted purely for meeting compliance standards while vulnerability testing is focused on online scans
-
Question 90:
What are the 6 core concepts in IT security?
A. Server management, website domains, firewalls, IDS, IPS, and auditing
B. Authentication, authorization, confidentiality, integrity, availability, and non-repudiation
C. Passwords, logins, access controls, restricted domains, configurations, and tunnels
D. Biometrics, cloud security, social engineering, DoS attack, viruses, and Trojans
Related Exams:
112-51
EC-Council Certified Network Defense Essentials (NDE)212-77
EC-Council Certified Linux Security212-81
EC-Council Certified Encryption Specialist (ECES)212-82
EC-Council Certified Cybersecurity Technician (C|CT)212-89
EC-Council Certified Incident Handler (ECIH)312-38
EC-Council Certified Network Defender (CND)312-39
EC-Council Certified SOC Analyst (CSA)312-40
EC-Council Certified Cloud Security Engineer (CCSE)312-49
ECCouncil Computer Hacking Forensic Investigator (V9)312-49V10
EC-Council Certified Computer Hacking Forensic Investigator (V10)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your ECSAv8 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.