Exam Details
Exam Code
:200-201Exam Name
:Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)Certification
:CyberOps AssociateVendor
:CiscoTotal Questions
:406 Q&AsLast Updated
:Mar 30, 2025
Cisco CyberOps Associate 200-201 Questions & Answers
-
Question 331:
Refer to the exhibit. What is the logical source device for these events?
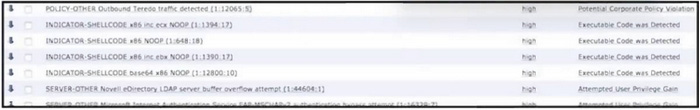
A. proxy server
B. IDS/IPS
C. NetFlow collector
D. web server
-
Question 332:
What is a Heartbleed vulnerability?
A. denial of service
B. information disclosure
C. buffer overflow
D. command injection
-
Question 333:
What are two types of cross site scripting attacks? (Choose two.)
A. directed
B. encoded
C. reflected
D. stored
E. cascaded
-
Question 334:
Which piece of information is needed for attribution in an investigation?
A. attack surface and the threat posing the risk
B. attack vector and exploited vulnerability
C. asset value and an asset owner
D. threat actor and associated behavior
-
Question 335:
What is the impact of a ransomware infection?
A. Data on infected endpoints is encrypted.
B. Encrypted data cannot be restored from backup.
C. Multiple connections are made to external CandC servers.
D. User must pay ransom to decrypt data.
-
Question 336:
According to CVSS, which metric group does user interaction belong to?
A. temporal
B. temporary
C. base
D. environmental
-
Question 337:
Refer to the exhibit. Which type of evidence is this file?
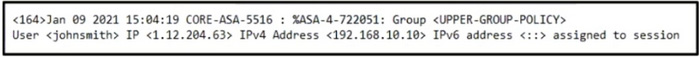
A. direct evidence
B. corroborating evidence
C. best evidence
D. circumstantial evidence
-
Question 338:
What is used to maintain persistent control of an exploited device?
A. encryption
B. ARP spoof
C. rootkit
D. DDoS
-
Question 339:
What is email greylisting by the mail transfer agent?
A. denying any email from a sender it does not recognize
B. returning emails that are potential phishing attempts
C. allowing emails from unknown senders temporarily
D. quarantining emails sent from outside of the organization
-
Question 340:
Refer to the exhibit.
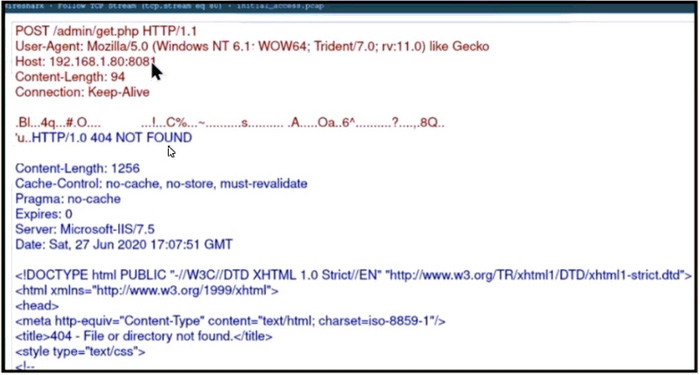
A security analyst received a ticket about suspicious traffic from one of the workstations. During the investigation, the analyst discovered that the workstation is communicating with an external IP The analyst was not able to investigate further and escalated the case to a T2 security analyst. What are the two data visibility challenges that the security analyst should identify? (Choose two.)
A. A default user agent is present in the headers.
B. Traffic is not encrypted.
C. Encrypted data is being transmitted.
D. POST requests have a "Microsoft-IIS/7.5" server header.
E. HTTP requests and responses are sent in plaintext.
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Cisco exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 200-201 exam preparations and Cisco certification application, do not hesitate to visit our Vcedump.com to find your solutions here.