Exam Details
Exam Code
:200-201Exam Name
:Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)Certification
:CyberOps AssociateVendor
:CiscoTotal Questions
:406 Q&AsLast Updated
:Mar 30, 2025
Cisco CyberOps Associate 200-201 Questions & Answers
-
Question 341:
Refer to the exhibit. What is occurring?
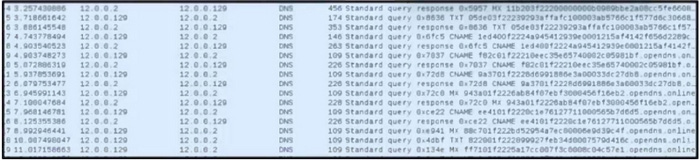
A. possible DNS amplification attack with requests that maximize data quantity
B. possible DNS tunneling with encrypted communication through CNAMEs
C. possible DNS cache poisoning with misdirects toward a fraudulent website
D. possible botnet traffic with random MX querying to generate increased traffic
-
Question 342:
Refer to the exhibit.
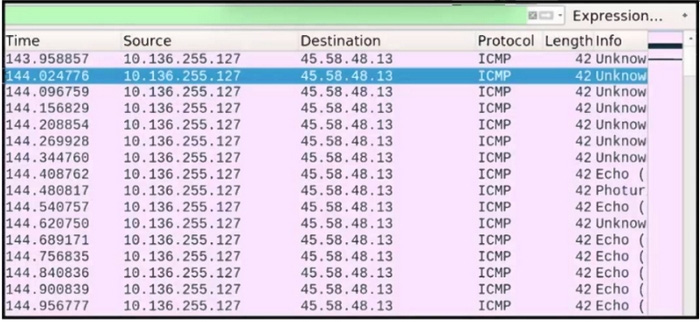
A network engineer is analyzing a network activity within captured traffic. An engineer notices suspicious behavior, a type of ICMP that Wireshark does not recognize. What is occurring?
A. These are failed communication attempts because ICMP communication is administratively prohibited.
B. These are responses from destination because the destination network is unreachable for this type of service.
C. Wireshark cannot map the type of ICMP requests because they are not legitimate ICMP echo requests.
D. Wireshark cannot map the type due to fragmentation, and fragment ID was not set on the destination host.
-
Question 343:
What are two differences of deep packet inspection compared to stateful firewall inspection? (Choose two.)
A. static lists for maintaining a strict access control level
B. different rule configurations based on payload pattern
C. quality of service capabilities based on list definitions
D. offers application-level monitoring
E. inspection of only the first packet during a connection attempt
-
Question 344:
What are the two differences between vulnerability and exploit? (Choose two.)
A. Vulnerabilities can be found in hardware and software, and exploits can be used only for software-based vulnerabilities.
B. Zero-day exploit can be used to take advantage of a vulnerability until the vulnerable software or hardware is patched.
C. Known vulnerabilities are assigned special CVE numbers, and exploits are using process to take advantage of vulnerabilities.
D. Zero-day exploit can be used for taking advantage of a known vulnerability, and cyber-attack can be performed on company assets.
E. Vulnerabilities are usually populated in the dark web, and exploit tools and methods can be found in the public web.
-
Question 345:
What is a comparison between rule-based and statistical detection?
A. Statistical is based on measured data while rule-based uses the evaluated probability approach.
B. Statistical uses the probability approach while rule-based is based on measured data.
C. Rule-based is based on assumptions and statistical uses data known beforehand.
D. Rule-based uses data known beforehand and statistical is based on assumptions.
-
Question 346:
Which evasion method is being used when TLS is observed between two endpoints?
A. encryption
B. obfuscation
C. X.509 certificate authentication
D. traffic insertion
-
Question 347:
Refer to the exhibit.
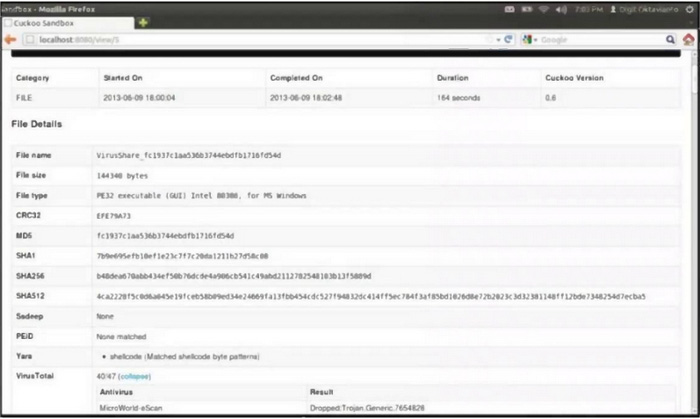
What does this Cuckoo sandbox report indicate?
A. The file is ransomware.
B. The file is spyware.
C. The file will open unsecure ports when executed.
D. The file will open a command interpreter when executed.
-
Question 348:
What is the purpose of a SIEM solution?
A. to collect and forward event logs to another log collection device to evaluate security threats
B. to collect and correlate event log data to provide holistic views of the security posture of an environment
C. to collect and categorize indicators of compromise to evaluate and search for potential security threats
D. to monitor and manage firewall access control lists for duplicate firewall filtering
-
Question 349:
Which example represents the defense-in-depth principle?
A. implementing a CMDB
B. creating a separate VLAN to isolate networks
C. creating a privileged group in AD
D. implementing new security policy within the organization
-
Question 350:
What is a difference between SIEM and SOAR security systems?
A. SOAR ingests numerous types of logs and event data infrastructure components, and SIEM can fetch data from endpoint security software and external threat intelligence feeds.
B. SOAR collects and stores security data at a central point and then converts it into actionable intelligence, and SIEM enables SOC teams to automate and orchestrate manual tasks.
C. SIEM raises alerts in the event of detecting any suspicious activity, and SOAR automates investigation path workflows and reduces time spent on alerts.
D. SIEM combines data collecting, standardization, case management, and analytics for a defense-in-depth concept, and SOAR collects security data, antivirus logs, firewall logs, and hashes of downloaded files.
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Cisco exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 200-201 exam preparations and Cisco certification application, do not hesitate to visit our Vcedump.com to find your solutions here.