Exam Details
Exam Code
:200-201Exam Name
:Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)Certification
:CyberOps AssociateVendor
:CiscoTotal Questions
:406 Q&AsLast Updated
:Mar 30, 2025
Cisco CyberOps Associate 200-201 Questions & Answers
-
Question 371:
How is SQL injection prevented?
A. sanitize user input
B. address space layout randomization
C. run the web server as a nonprivileged user
D. host profiling
-
Question 372:
Which type of data is used to detect anomalies in the network?
A. statistical data
B. metadata
C. transaction data
D. alert data
-
Question 373:
What is data encapsulation?
A. Data is encrypted backwards, which makes it unusable.
B. Multiple hosts can be supported with only a few public IP addresses.
C. A protocol of the sending host adds additional data to the packet header.
D. Browsing history is erased automatically with every session.
-
Question 374:
Which type of attack uses a botnet to reflect requests off of an NTP server to overwhelm a target?
A. replay
B. distributed denial of service
C. denial of service
D. man-in-the-middle
-
Question 375:
An analyst performs traffic analysis to detect suspicious activity and identifies the multiple UDP connections through the same port. Which technology makes this behavior feasible?
A. TOR
B. ACL
C. P2P
D. NAT
-
Question 376:
Which security monitoring data type is associated with application server logs?
A. transaction data
B. statistical data
C. session data
D. alert data
-
Question 377:
What is the impact of encryption on data visibility?
A. TLS 1.3 traffic cannot be decrypted and monitored.
B. Traffic decryption causes high CPU load on monitoring systems.
C. Traffic decryption is needed for deep inspection of SSL traffic via NGFW.
D. IPsec encryption of traffic is vulnerable to man-in-the-middle attacks.
-
Question 378:
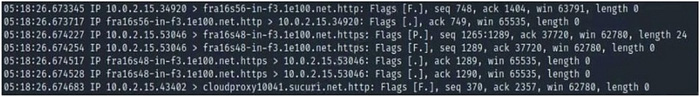
What can be identified from the exhibit?
A. NetFlow data
B. spoofed TCP reset packets
C. DNS hijacking
D. tcpdump data
-
Question 379:
What is a description of a man-in-the-middle network attack?
A. After attackers penetrate a network, they can use privilege escalation to expand their reach.
B. Attackers build botnets, large fleets of compromised devices, and use them to direct false traffic at networks or servers.
C. It involves attackers intercepting traffic, either between a network and external sites or within a network.
D. Attackers replicate malicious traffic as legitimate and bypass network protection solutions.
-
Question 380:
Which two protocols are used for DDoS amplification attacks? (Choose two.)
A. HTTP
B. DNS
C. TCP
D. ICMPv6
E. NTP
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Cisco exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 200-201 exam preparations and Cisco certification application, do not hesitate to visit our Vcedump.com to find your solutions here.